Aegis, our agent program
(software that communicates between your server and our system)
will work on all, Linux and windows based machines, including virtual server.
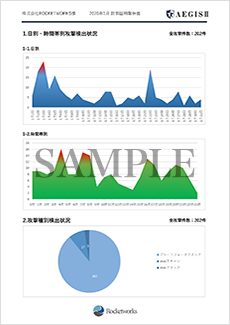
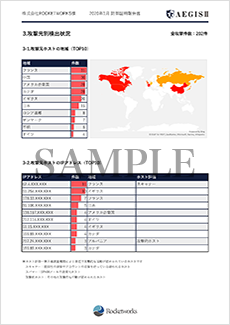
"Aegis" checks all communications to your server, log data are send to our cloud system (main system) by AES encrypted communication, and realizes real time security.
Therefore, as you may understand from the above description, the number of hosts, servers and the type of web server software does not affect our system to detect attacks, as long as the logs are in a format that Aegis supports.
※ If any IP address or signature pattern is detected as an attacker, our data center will order Aegis, our agent program installed to your server, to stop only the detected communication notified through the logs.
※ Aegis is very small and simple. The size is only about one floppy disc so you don't have to worry about the capacity of your server. The CPU occupation remains below 1% and you don't even need to reboot your system.